The Health Insurance Portability and Accountability Act of 1996 (or HIPAA for short) is a broad status that covers five Titles. Title two, “Preventing Health Care Fraud and Abuse; Administrative Simplification; Medical Liability Reform”, establishes (among other things) policies and procedures for maintaining the privacy and the security of individually identifiable health information.
Our Customer’s Core Requirements
One of our customers, a Research Laboratory in Harvard, was looking for help revisiting and implementing security controls for one of their lab workloads. Our customer was looking to implement TLS as a part of their Web application stack for user-facing APIs.
Before implementing the TLS or provide any recommendations, we made a careful architecture analysis beforehand. Unfortunately, the customer was using Amazon Elastic Load Balancer (ELB) at the time. As the TLS configuration on an Elastic Load Balancer is somewhat limited, the OCSP Stapling, along with some other features, was not supported (as of the writing of this article). ELB is a straightforward service out of the box but with substantial limitations to match the specific SSL/TLS requirements. ELB comes with default configuration, and it does not provide complete control over some key parameters, such as DH parameters, SPDY and NPN support, choice of elliptic curve algorithm, secure client-initiated renegotiation, and so on. Since some of the TLS features that our customer was requiring were not supported by the ELB, we suggested a different solution and a strategy.
Custom TLS implementation on AWS with Nginx
We sit together with the Lab engineering team, answering questions and brainstorming on their Slack channel. By working together, we have implemented the solution using Nginx as a proxy handling SSL/TLS traffic.
We are very familiar with using Nginx and its SSL/TLS configuration and have a lot of experience building reliable proxies for our customers in the past.
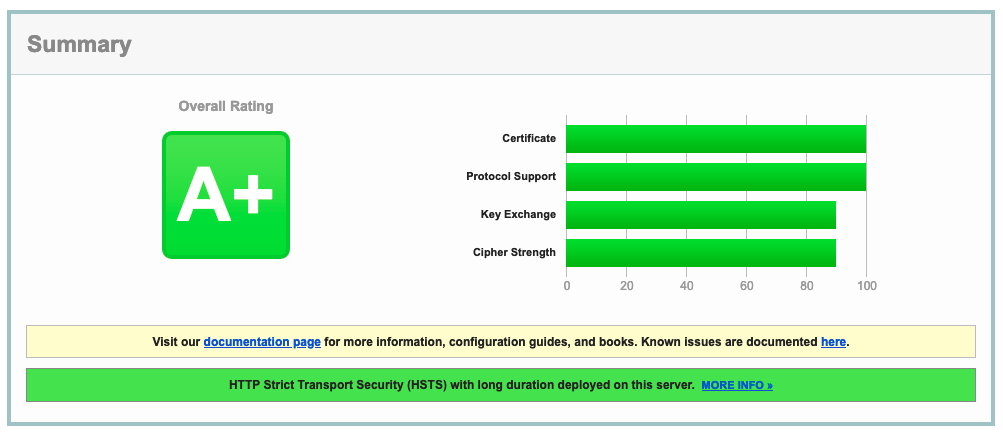
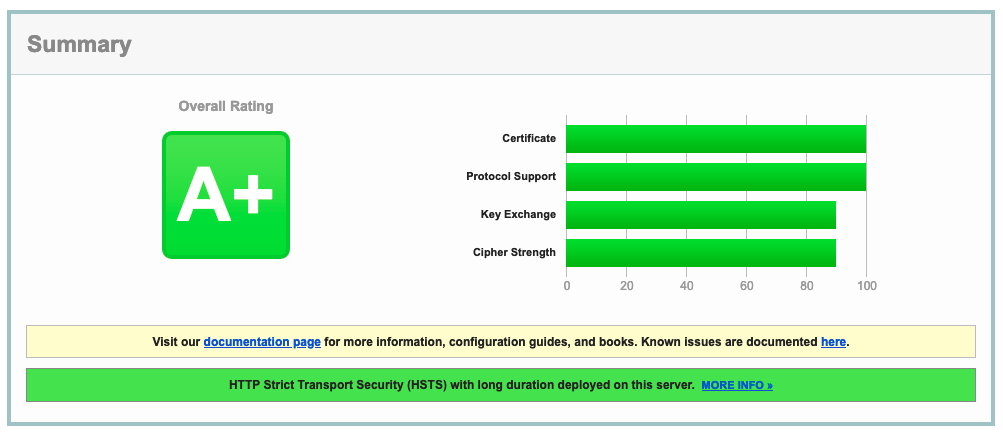
The solution was placed behind the ELB, and the whole application stack was rebuilt with autoscaling capabilities. With autoscaling capabilities, it would spun-up the application server. Each server then would mount an Elastic Network File System storing SSL/TLS certificates and related configuration. It worked great! Having complete control over the TLS settings, we fine-tuned the solution to achieve our customer business objective. We got an A+ rating for SSL/TLS configuration as reported by the conventional industry vendors, such as Qualys.
Thank You
Thank you for your trust and an incredible experience. We look forward to staying in touch, whether a further project engagement or a stop-by to say Hello.